

MY RESEARCH INTEREST.
- Anonymous Communication and privacy-enhancing technologies
- Cryptography; specifically cryptanalysis
- Pattern Recognition and Classification of images and documents
- Machine learning

WELCOME TO MY WEB PAGE!


Thanks for watching my Presentation on Tor usage and challenges. If you have any comment, please feel free to contact me.
Introduction to Tor video: Click here to play
presentation on Tor usage: Click here to play
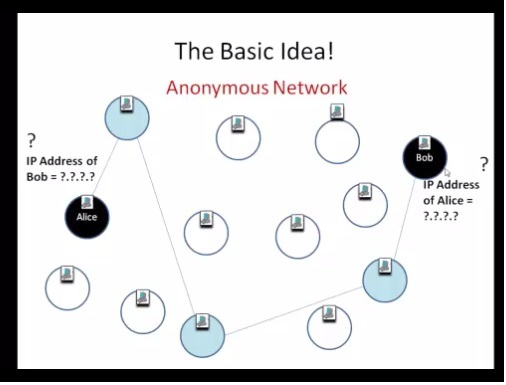
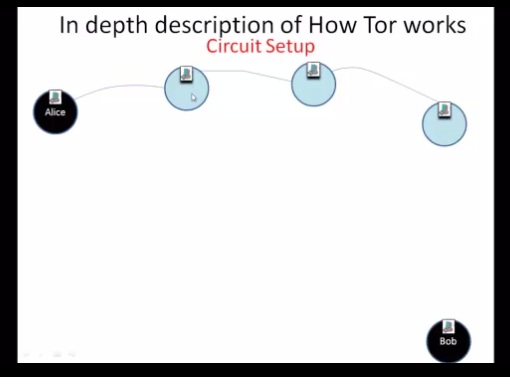
Basic idea of anonymity system and Tor circuit setup: click here to play
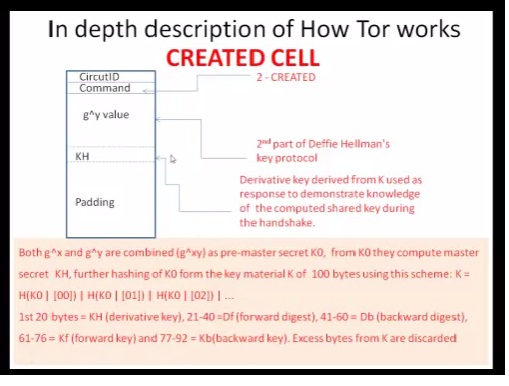
In-depth description of circuit set up and components: click here to play
In-depth description of Circuit setup: click here to play
Challenges of runing Tor exit node: click here to play
REPORTS
- In-depth technical description on how Tor works (part of my thesis work).
- Reports on Port forwarding and Redirection (part of my thesis work).
- Reports on Network application Architecture (part of my thesis work).
- Survey on Cryptanalysis submitted as term paper during data encryption course
- Technical report on setting up experimenTor (part of my thesis work)
- Report on Arabic bank check feature extraction and classification submitted to ARHAT group
- Manual on how to use corpus based Arabic spelling checker program submitted to ARHAT group